Quiet Persistence: How China's Cyber Strategy Has Turned Critical Infrastructure Into a Contingent Liability for Every Portfolio That Owns It
The People's Liberation Army does not need to fire a shot to reprice your infrastructure portfolio.
Volt Typhoon, a People's Republic of China (PRC)-sponsored advanced persistent threat (APT) group, has spent at least five years pre-positioning inside the operational technology (OT) networks of US and allied critical infrastructure.
It is not stealing data. It is installing optionality: the capacity to trigger cascading disruption at a moment of geopolitical choice. We as an investment community need to think about how to price in this uncertainty.
Why This Matters
Confirmed pre-positioning: CISA, the FBI and the NSA have confirmed Volt Typhoon has access inside energy, water, transport and communications networks across the US and Five Eyes partners, including the UK, with dwell times traced to 2019 or earlier.
Uninsured contingent liability: This is not a conventional cyber incident. It is an embedded liability in critical infrastructure equity and debt for which war exclusion clauses are systematically eliminating insurance cover.
Policy response accelerating: Regulation is tightening on both sides of the Atlantic, creating compliance cost for portfolio companies and a structural capital opportunity in defence-grade OT resilience.
From Espionage to Option Value
What distinguishes Volt Typhoon from most threat actors is intent. The group was first publicly named by Microsoft and US agencies in May 2023, and its links to PRC state direction were formally confirmed in a joint advisory from CISA, the FBI and the National Security Agency (NSA). Its defining technique is living-off-the-land (LOTL): using legitimate administrative tools already present on a network, such as PowerShell and Windows Management Instrumentation (WMI), rather than deploying custom malware. This makes forensic detection slow and attribution difficult, by design.
The sectors confirmed as targets include electric utilities, water and wastewater systems, oil and gas pipelines, maritime ports, and telecommunications. A further joint advisory published in April 2026, covering Volt Typhoon and Flax Typhoon, confirmed both groups remain active across multiple infrastructure verticals. Some dwell times inside compromised networks have been traced back to 2019 and, in certain cases, earlier. That is not reconnaissance. That is pre-positioning for a trigger that has not yet been pulled, most plausibly a military or political confrontation over Taiwan.
The Mechanism Consensus Has Missed
The standard analytical frame treats Volt Typhoon as a cybersecurity problem to be managed by IT departments. The more accurate read is that Beijing has acquired, at relatively low cost, a contingent disruption capability against US and allied economies. It can impose significant economic damage without crossing the legal threshold for an armed attack under international law. The ambiguity is deliberate.
The Bank of England's 2025 CBEST thematic report, published in January 2026 and co-authored with the National Cyber Security Centre (NCSC), explicitly cited Volt Typhoon in its technical guidance, noting the group "gained initial access by exploiting privilege escalation vulnerabilities" and "relied on valid credentials for persistence." The NCSC framed the group's LOTL techniques as the direct rationale for network segregation requirements across the UK financial sector. That a central bank regulator has embedded a specific PRC APT into its financial sector resilience testing framework is a regulatory signal that has not yet found its way into asset pricing.
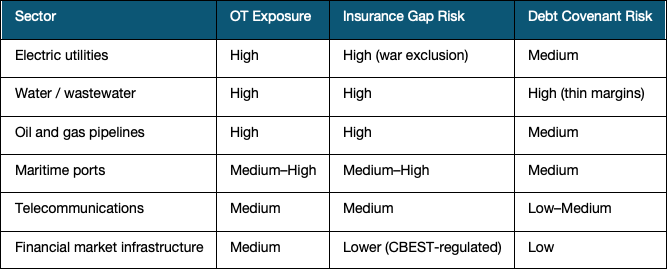
Who Absorbs the Risk
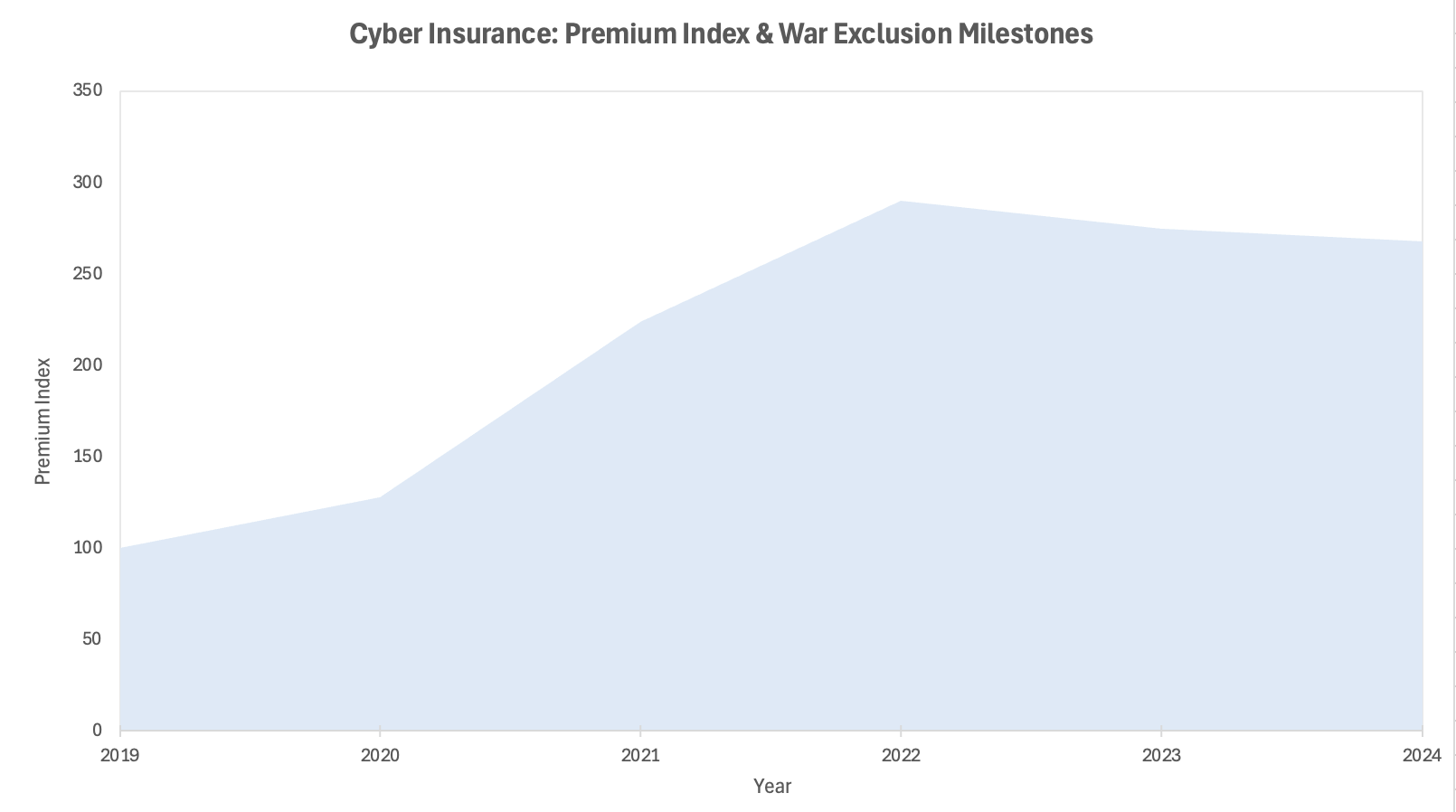
Infrastructure equity holders carry the first-order exposure. A successful disruption of an electric utility or water network does not generate a clean insurance claim: it creates revenue interruption, regulatory penalty, potential physical asset write-down, and prolonged reputational damage. The problem is structural. Cyber insurance policies are progressively excluding nation-state attacks under war exclusion clauses. The Merck v. ACE American litigation, settled in 2023, established the legal perimeter of this exclusion; Lloyd's of London subsequently mandated war exclusion language for all standalone cyber policies from March 2023. The more likely read for most OT-heavy infrastructure portfolios is that a meaningful portion of tail risk is currently uninsured, unpriced, and misattributed in standard risk models as regulatory or climate risk.
Infrastructure debt holders face a distinct but related exposure. A prolonged outage or a forced accelerated capex cycle to remediate compromised OT systems could stress interest coverage ratios and trigger covenant renegotiation, particularly in the leveraged structures common in mid-market infrastructure private credit. The sectors most vulnerable are those with the heaviest OT footprint and weakest cyber investment relative to total capex: water utilities, smaller regional electric co-operatives, and port operators.
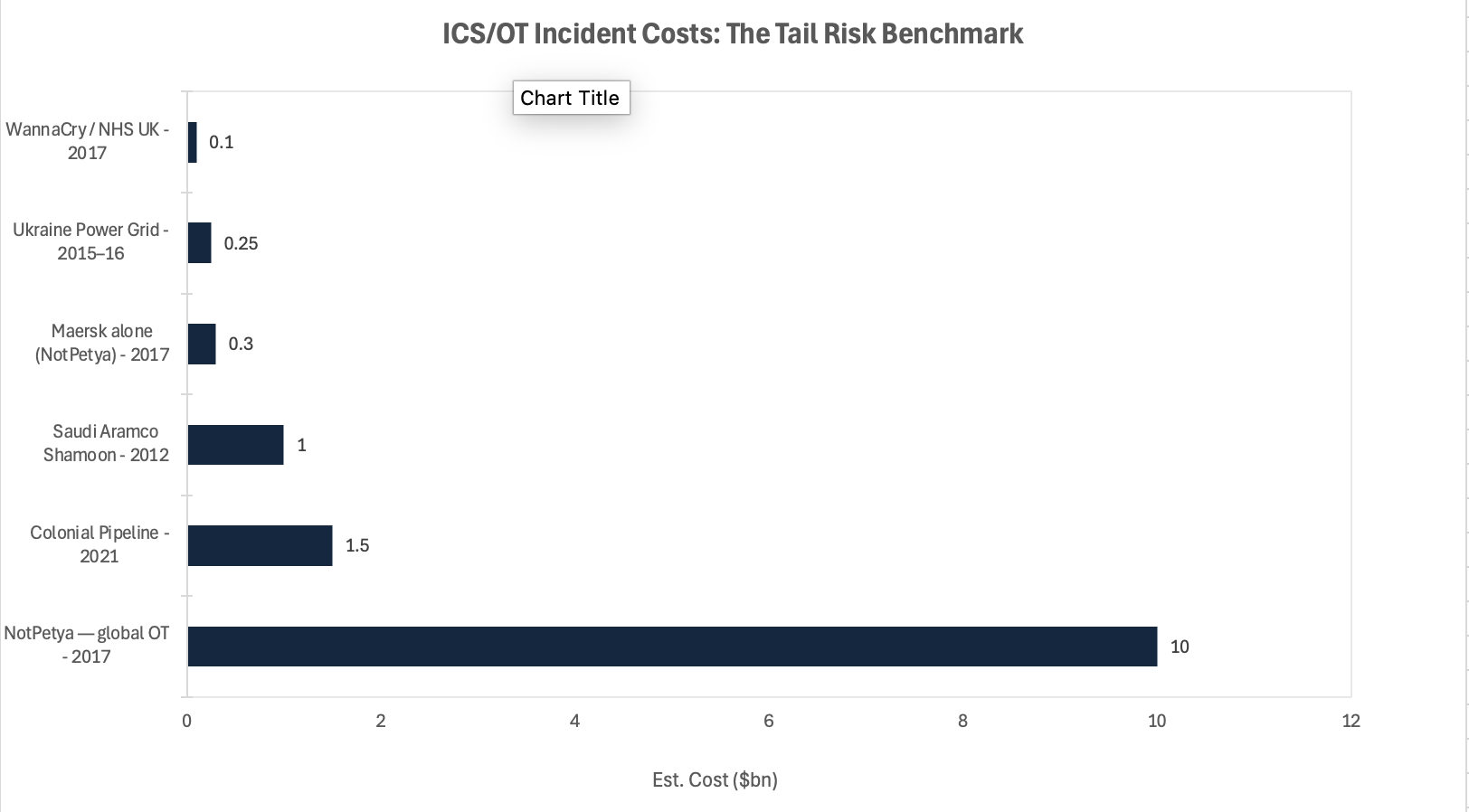
Chart 1 — Selected ICS/OT incidents illustrate the tail-risk quantum Volt Typhoon pre-positioning could activate. Colonial Pipeline's $1.5bn estimated economic impact and NotPetya's $10bn global toll represent the range. Sources: US government reports, Maersk annual filings, industry estimates.
Near-Term Catalysts and Policy Outlook
The risk asymmetry here is not symmetric: the downside of inaction compounds faster than any compliance burden of preparation. Regulatory pressure is building on a convergent timeline across multiple jurisdictions, and the gap between when policy signals and when asset pricing adjusts is where the exposure sits.
0–3 months: The April 2026 CISA/FBI/NSA joint advisory is likely to accelerate final rulemaking under the US Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA), with implementing rules expected before the end of 2026. In the UK, the Cyber Security and Resilience Bill is in active parliamentary passage, extending mandatory incident reporting and resilience obligations to a broader set of infrastructure operators and their digital supply chains. Both developments add near-term compliance cost to portfolio companies and will increasingly surface as a material factor in M&A due diligence processes.
3–12 months: Larger institutional infrastructure managers are beginning to integrate OT cyber resilience scoring into due diligence frameworks, following the trajectory set by the Bank of England's CBEST programme and the EU's Digital Operational Resilience Act (DORA). Assets without documented OT network segmentation and an auditable threat response capability will face a growing discount in secondary market transactions. The direction of regulatory travel is now clear enough that this is a valuation question, not just a compliance one.
How this resolves depends less on Volt Typhoon itself than on the geopolitical temperature around Taiwan and the credibility of allied deterrence signalling over the next twelve months. Three broad paths are plausible.
Base case: Volt Typhoon maintains pre-positioned access without triggering disruption. Compliance cost rises steadily; cyber security becomes a standard infrastructure capex line. Risk premiums on critical infrastructure assets widen modestly, broadly absorbed by regulatory tariff frameworks.
Upside: A coordinated Five Eyes attribution campaign forces meaningful PRC restraint. Risk premium compresses; cyber-resilient infrastructure operators trade at a structural premium over peers.
Downside: A geopolitical trigger over Taiwan prompts selective activation of pre-positioned access. Targeted disruption of grid or port operations cascades into insurance disputes, credit stress, and a rapid repricing of infrastructure equity and related private debt.
Chart 2 — Cyber insurance premium index (2019=100) showing the hardening cycle and key war exclusion milestones. Nation-state attack exclusions have progressively narrowed coverage available to critical infrastructure operators. Sources: CIAB, Lloyd's of London, Marsh.
Conclusion
The mistake is to frame Volt Typhoon in the language of incidents. An incident has a start and an end; it is remediated, claimed, and priced. What Volt Typhoon represents is structural: a persistent change in the risk profile of an asset class that the market has long priced as low-volatility, long-duration, and geopolitically neutral. None of those assumptions hold without qualification.
The US Intelligence Community's 2025 Annual Threat Assessment identified China's cyber operations as the pre-eminent threat to US critical infrastructure. The Bank of England's CBEST 2025 thematic made Volt Typhoon a named scenario for UK financial sector resilience testing. That convergence of intelligence community assessment and central bank regulatory practice is the structural signal. Allocators who treat this as an IT procurement question will be behind when the repricing arrives. Those who integrate it into capital allocation now, by adjusting discount rates for OT-heavy infrastructure, scrutinising war exclusion language across existing portfolio insurance, and identifying the companies building defence-grade OT resilience, will have positioned correctly before the market has fully caught up.
References
CISA, FBI, NSA — Joint Cybersecurity Advisory: Volt Typhoon — May 2023
CISA, FBI, NSA — Joint Advisory: Volt Typhoon and Flax Typhoon Botnets — April 2026
Bank of England, PRA, FCA, NCSC — 2025 CBEST Thematic — January 2026
Microsoft Threat Intelligence — Volt Typhoon Targets US Critical Infrastructure — May 2023
US Office of the Director of National Intelligence — Annual Threat Assessment 2025
Lloyd's of London — Market Bulletin: War Exclusion for Standalone Cyber — 2022–2023
Merck & Co v. ACE American Insurance — New Jersey Superior Court — Settled 2023
UK Parliament — Cyber Security and Resilience Bill — 2024–26 Session
Council of Insurance Agents and Brokers (CIAB) — Cyber Insurance Market Reports 2019–2024
Marsh — Cyber Insurance Pricing Index — 2021–2024
The Conversation — "What is Volt Typhoon?" — March 2024
This article is for information and discussion only and does not constitute investment advice or a recommendation.